Java API authentication can rely on session-based mechanisms, API keys, OAuth 2.0 flows, or HMAC signing to provide robust security without requiring JWT implementation complexities, offering developers practical alternatives that integrate seamlessly with existing infrastructure and frameworks like Spring Security.
If you've ever struggled with Java API authentication that actually works without JWT headaches, you're not alone. Many developers find themselves wrestling with token expiration, signature validation, and library incompatibilities when implementing JWT-based systems. The good news? Several proven authentication methods deliver enterprise-grade security without the JWT learning curve, and they're already battle-tested in production environments across Brazil and worldwide.
Why developers look beyond JWT for API authentication
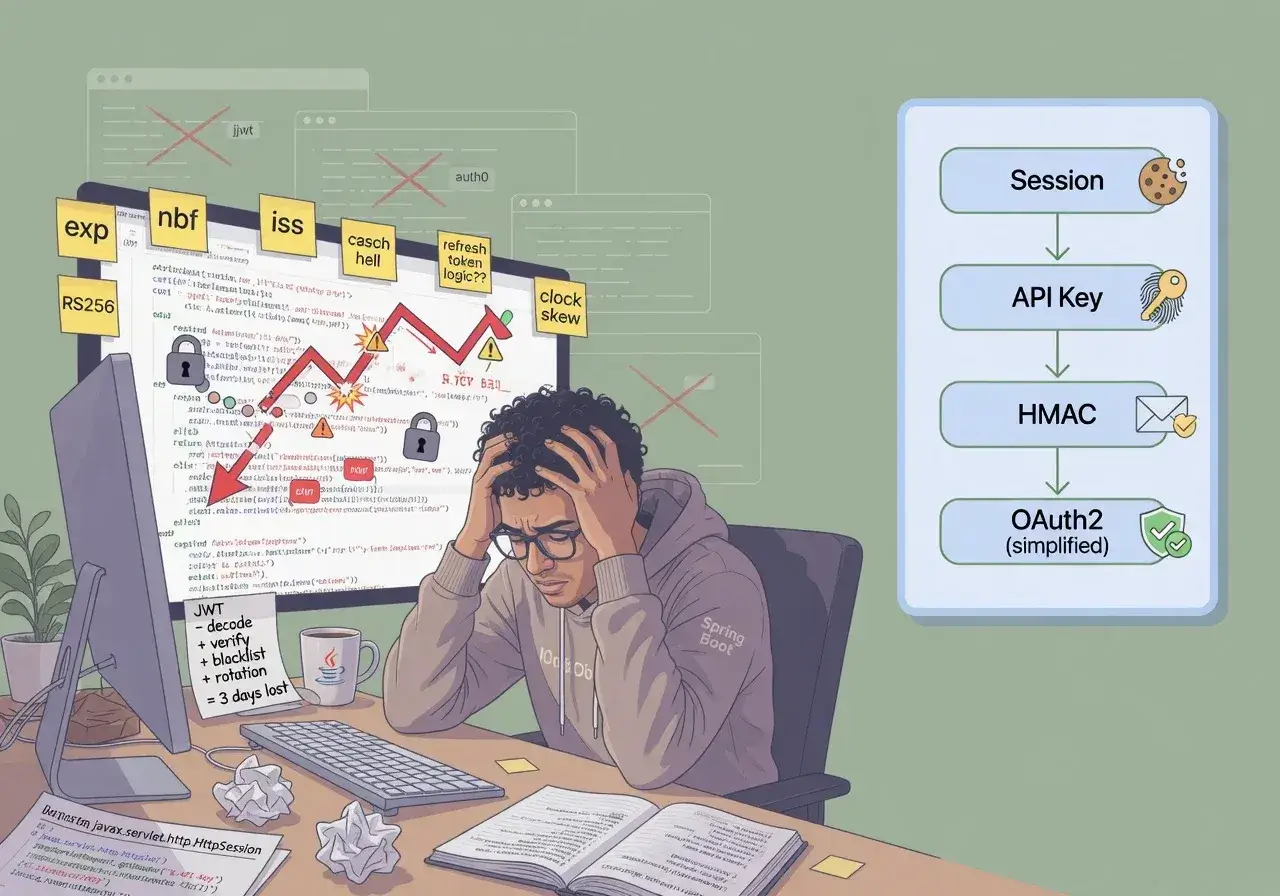
JWT has become synonymous with modern API security, but it introduces complexity that doesn't always match project requirements. Token size, stateless validation challenges, and revocation difficulties create friction points that slow development cycles.
Traditional authentication approaches offer tangible benefits for specific use cases. Session-based authentication works exceptionally well for monolithic applications or microservices within trusted network boundaries. API keys provide straightforward authentication for server-to-server communication without requiring cryptographic operations on every request.
The choice between JWT and alternatives depends on your architecture, team expertise, and security requirements. Understanding what each method brings to the table helps you make informed decisions rather than following trends blindly.
Session-based authentication with Spring Security
Spring Security offers mature session management that handles authentication state server-side, eliminating token parsing overhead and simplifying security logic across your application layers.
Implementation essentials
Configuring session authentication requires minimal setup in Spring Boot applications. The framework manages session creation, validation, and destruction automatically through servlet containers.
- HttpSession stores user credentials and roles securely on the server
- JSESSIONID cookies maintain session continuity across requests
- Built-in CSRF protection guards against cross-site attacks
- Session fixation protection prevents hijacking attempts
This approach works particularly well for applications serving web clients and mobile apps that can maintain cookie state. Redis or Hazelcast integration enables session sharing across multiple server instances, addressing scalability concerns that often push teams toward stateless tokens.
API key authentication for service integration
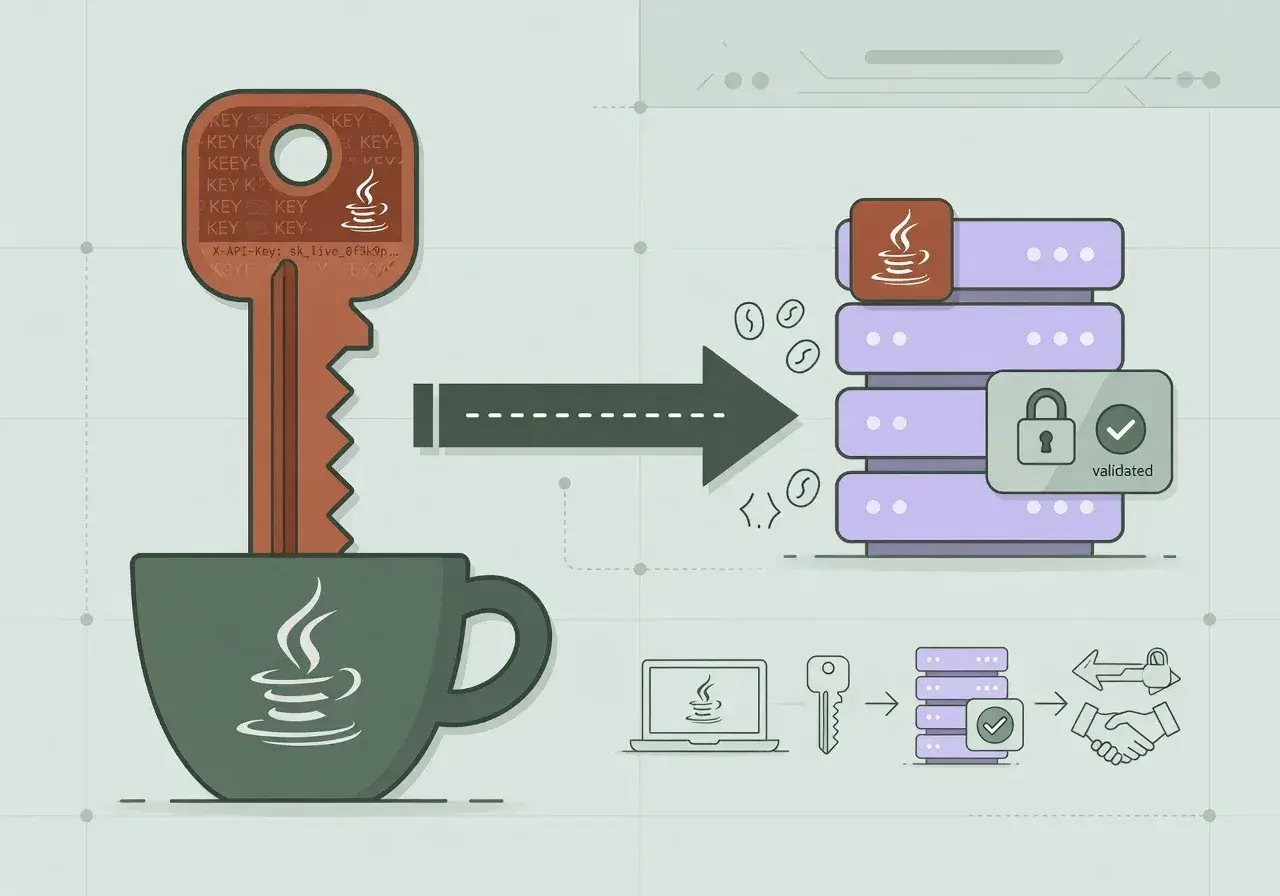
API keys provide the simplest authentication mechanism for machine-to-machine communication, requiring only header validation without cryptographic operations or token lifecycle management.
Generating unique keys per client application allows granular access control and usage tracking. Store hashed versions in your database using BCrypt or Argon2, never plain text. Implement rate limiting per key to prevent abuse and monitor usage patterns for anomaly detection.
Security considerations
- Rotate keys periodically to limit exposure windows
- Use HTTPS exclusively to prevent key interception
- Implement IP whitelisting for additional protection layers
- Log all authentication attempts for audit trails
API keys excel in scenarios where you control both client and server, such as internal microservices or partner integrations with established trust relationships. They eliminate token refresh logic and reduce network overhead compared to OAuth flows.
OAuth 2.0 without JWT tokens
OAuth 2.0 supports opaque access tokens that reference server-side session data rather than encoding claims within the token itself, combining OAuth's authorization framework with session-based simplicity.
Spring Authorization Server and Keycloak both support opaque token generation. Clients receive random strings that map to authorization grants stored in the authorization server's database. Resource servers validate tokens through introspection endpoints rather than local verification.
This model centralizes token revocation since the authorization server controls validity. When a user logs out or administrators revoke access, the change takes effect immediately without waiting for token expiration. The trade-off involves additional network calls for token validation, which caching strategies can mitigate effectively.
HMAC signature authentication
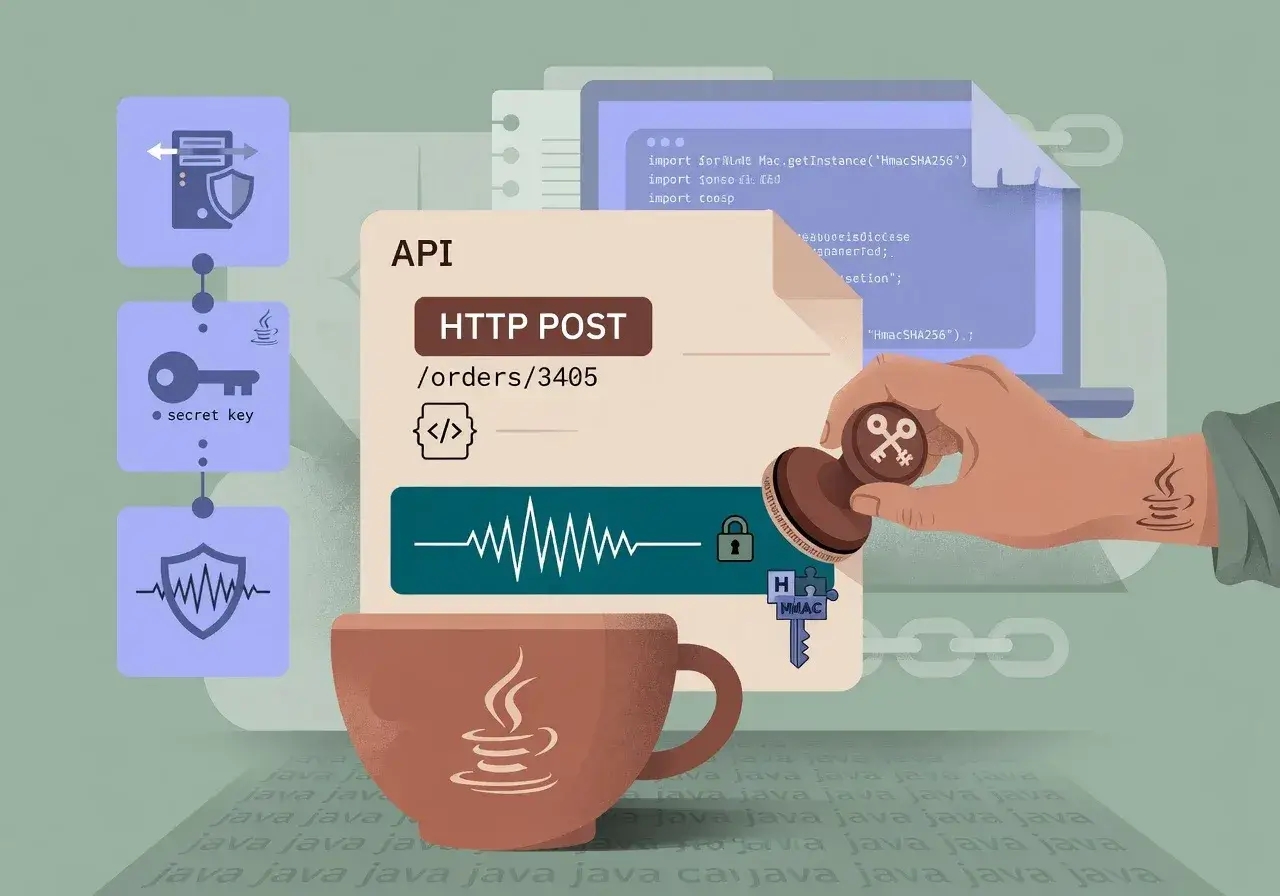
HMAC-based authentication signs requests using shared secrets, providing cryptographic proof of authenticity without token overhead or expiration management complexities.
Building HMAC authentication
Clients generate signatures by hashing request components—method, path, timestamp, body—with a secret key. Servers recompute the signature using the same algorithm and compare results to verify authenticity.
- Include timestamps to prevent replay attacks
- Sign the complete request payload to ensure integrity
- Use SHA-256 or stronger hashing algorithms
- Implement signature validation in servlet filters
AWS and many payment processors use HMAC authentication for their APIs, demonstrating its reliability at scale. Implementation requires careful attention to clock synchronization and signature string construction, but eliminates token storage and refresh logic entirely.
Basic authentication with modern enhancements
HTTP Basic Authentication, when combined with HTTPS and proper credential management, offers surprising utility for internal tools and development environments where simplicity outweighs sophisticated authorization needs.
Encode credentials in Base64 within the Authorization header, letting Spring Security handle validation against your user database. Add account lockout mechanisms after failed attempts and implement strong password policies to address Basic Auth's traditional weaknesses.
Consider Basic Auth for administrative interfaces, internal dashboards, or development APIs where user convenience and rapid implementation matter more than complex authorization rules. Always pair it with HTTPS and consider IP restrictions for additional security layers.
Choosing the right authentication strategy
No single authentication method suits every scenario. Session-based approaches work well for traditional web applications with server-side rendering. API keys simplify service-to-service communication within trusted boundaries. OAuth 2.0 with opaque tokens balances flexibility with centralized control.
Evaluate your specific requirements around scalability, security posture, client types, and team expertise. Consider hybrid approaches where different authentication methods serve different API endpoints based on their security requirements and usage patterns.
The authentication landscape extends far beyond JWT, offering proven alternatives that eliminate complexity while delivering robust security. Your choice should align with architectural realities rather than industry buzz.
Conclusion: practical authentication without JWT complexity
Java developers have multiple robust authentication options that avoid JWT's implementation challenges while providing enterprise-grade security. Session-based authentication, API keys, OAuth with opaque tokens, and HMAC signatures each address specific use cases effectively. By matching authentication mechanisms to your actual requirements rather than following trends, you build systems that are both secure and maintainable, letting your team focus on business logic instead of wrestling with token libraries and cryptographic edge cases.