API security vulnerabilities emerge when developers overlook three critical validation layers: input sanitization, authentication verification, and response filtering, creating exploitable gaps that attackers routinely target to compromise systems and extract sensitive data.
Your API security has a hole if you skip these 3 validation layers, and most development teams don't realize the damage until it's too late. APIs handle millions of requests daily, and without proper validation checkpoints, each request becomes a potential entry point for malicious actors. Understanding these layers isn't just technical housekeeping—it's the difference between a secure system and a data breach headline.
Why validation layers matter more than you think
APIs serve as the communication backbone between applications, but this connectivity creates vulnerability. Every unvalidated request carries risk, and attackers know exactly where to probe.
Security isn't about building walls—it's about creating intelligent filters that distinguish legitimate traffic from threats. The three validation layers work together as a defense system, each catching what the others might miss.
The real cost of skipping validation
Companies face average losses of $4.24 million per data breach, according to recent industry reports. Most breaches trace back to API vulnerabilities that proper validation would have prevented.
- Unauthorized data access leading to customer information exposure
- System manipulation through injection attacks
- Service disruption from malformed requests overwhelming servers
- Compliance violations resulting in regulatory fines
Layer one: Input sanitization stops attacks at the door
Input sanitization examines every piece of data entering your API before processing begins. This layer prevents injection attacks, buffer overflows, and malformed data from reaching your application logic.
Think of input sanitization as your first security checkpoint. It validates data types, checks string lengths, removes dangerous characters, and ensures requests match expected formats. Without this layer, attackers can inject SQL commands, script tags, or oversized payloads designed to crash your system.
Common input validation techniques
- Whitelist validation accepting only predefined safe inputs
- Data type enforcement ensuring integers stay integers and strings remain strings
- Length restrictions preventing buffer overflow attempts
- Special character filtering removing potentially dangerous symbols
Implementing input sanitization requires understanding your API's expected data patterns. Document what valid requests look like, then reject everything that deviates from these specifications.
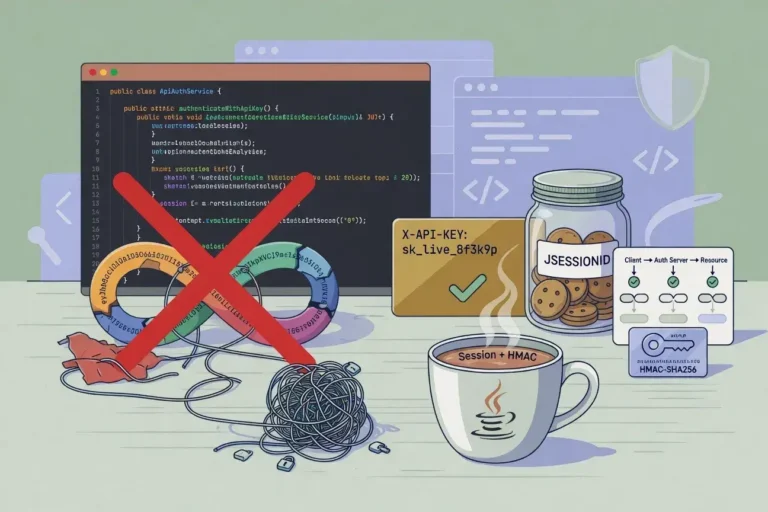
Layer two: Authentication verification confirms who's knocking
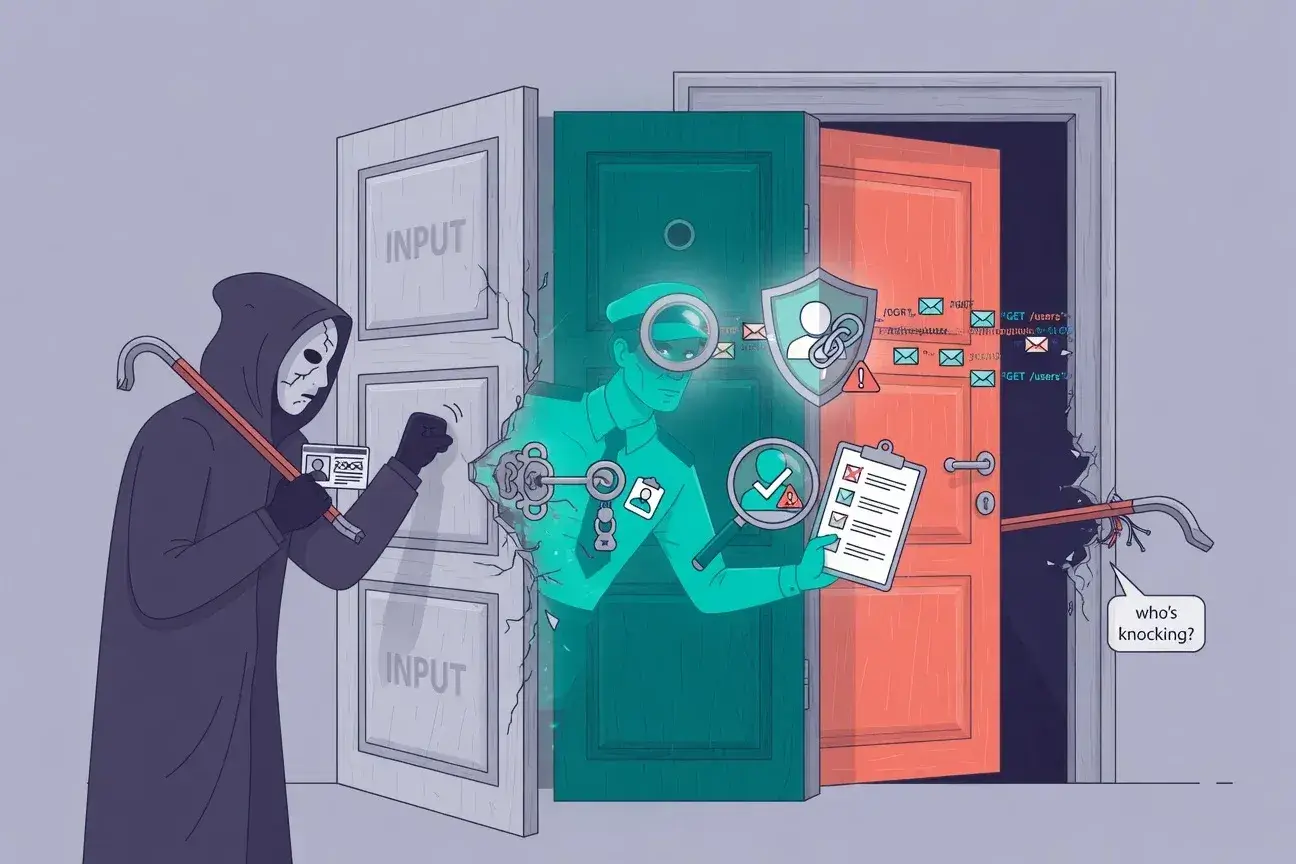
Authentication verification ensures requests come from legitimate sources with proper credentials. This layer prevents unauthorized access and maintains accountability for all API interactions.
Many developers implement basic authentication but fail to verify tokens properly, check expiration times, or validate permission scopes. Attackers exploit these gaps using stolen tokens, replay attacks, or privilege escalation techniques.
Essential authentication checks
Every request should undergo multiple authentication verifications. Check token validity, confirm expiration timestamps, validate signature integrity, and verify the requesting entity has appropriate permissions for the specific action.
- Token signature validation using cryptographic verification
- Expiration timestamp checking to prevent token reuse
- Permission scope verification matching actions to authorized roles
Authentication isn't a one-time check at login. Each API request requires fresh verification because tokens can be compromised, permissions can change, and sessions can be hijacked between requests.
Layer three: Response filtering protects sensitive data
Response filtering controls what information leaves your system. This often-overlooked layer prevents data leakage, information disclosure, and unintended exposure of system internals.
APIs frequently return more data than necessary, exposing database structures, internal IDs, or sensitive user information that shouldn't be visible. Attackers use this leaked information to map your system architecture and plan targeted attacks.
Response filtering strategies
- Field-level permissions showing only data the requester should access
- Error message sanitization hiding system details from potential attackers
- Rate limiting preventing information harvesting through repeated requests
- Response size monitoring detecting unusual data extraction attempts
Proper response filtering requires understanding data sensitivity levels and implementing granular controls that adapt based on requester identity and context.
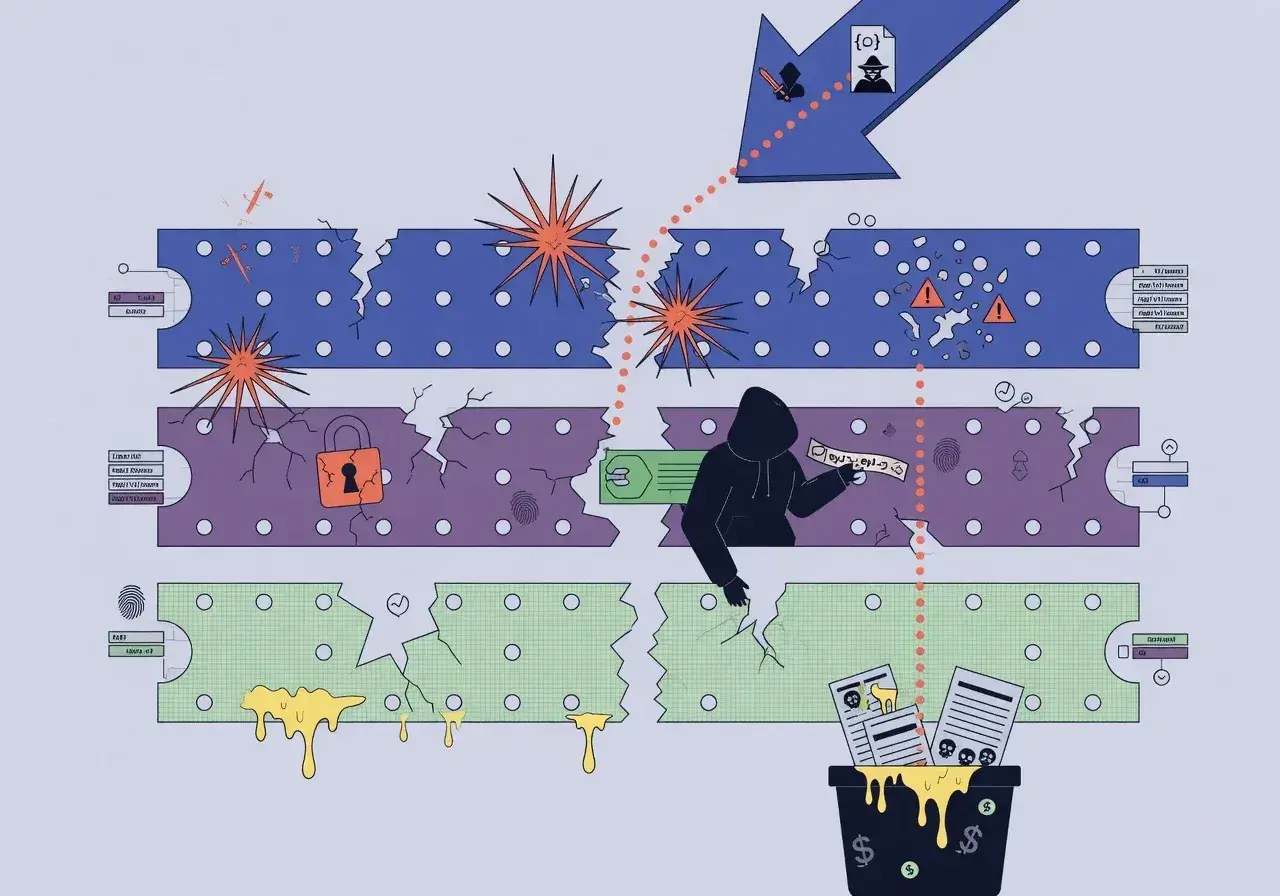
How these layers work together
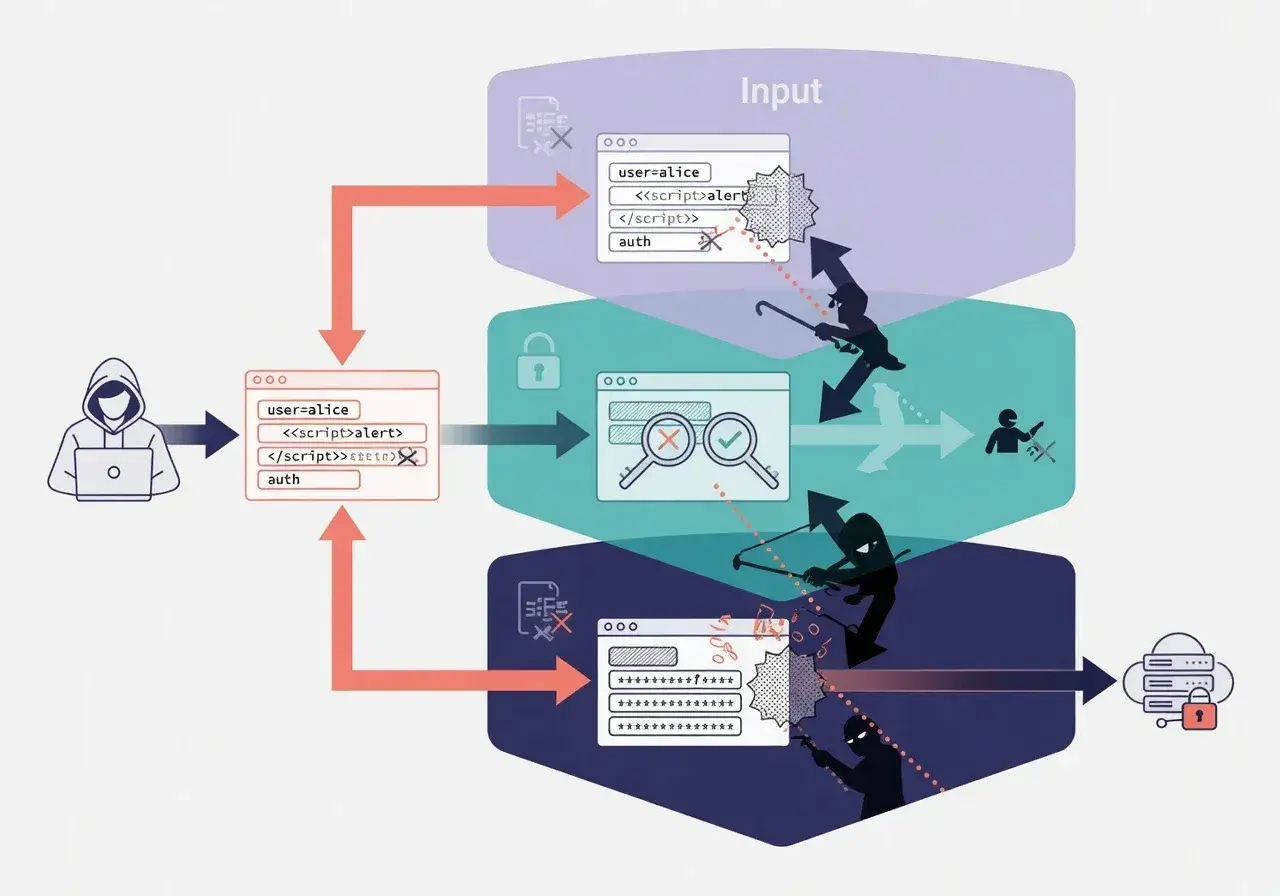
The three validation layers create overlapping security zones. Input sanitization catches malformed requests, authentication stops unauthorized users, and response filtering prevents data leakage even if earlier layers are bypassed.
This defense-in-depth approach means attackers must defeat multiple security mechanisms simultaneously. Each layer compensates for potential weaknesses in the others, creating a resilient security posture that adapts to evolving threats.
Implementing validation without killing performance
Security validation adds processing overhead, but smart implementation minimizes performance impact. Cache authentication results, use efficient validation libraries, and implement checks in parallel rather than sequentially.
Modern APIs handle thousands of requests per second while maintaining robust validation. The key is optimizing validation logic and using appropriate tools designed for high-throughput environments.
Performance optimization techniques
- Validation result caching for repeated similar requests
- Asynchronous processing for non-blocking security checks
- Early rejection patterns failing fast on obvious violations
Conclusion: Building unbreakable API security
API security demands comprehensive validation across input sanitization, authentication verification, and response filtering. Skipping any layer creates exploitable vulnerabilities that attackers will eventually discover. Implementing all three layers transforms your API from a potential liability into a secure, trustworthy system that protects both your organization and your users from increasingly sophisticated threats.